Protocol for Data Collection
1. Introduction & Ethical Approval
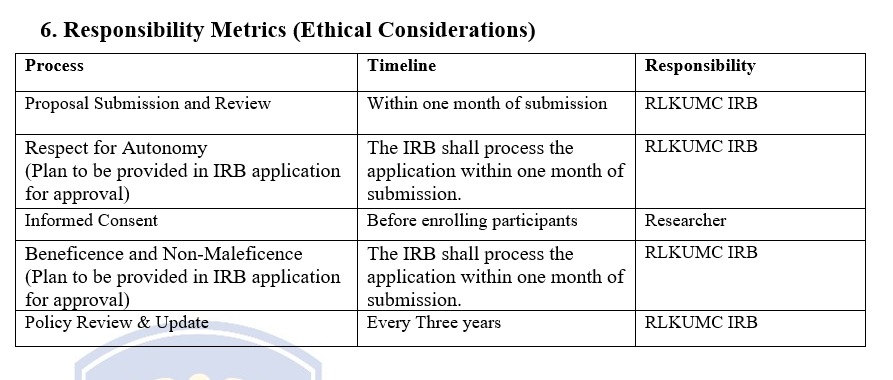
1.1 Researchers must obtain approval from the RLKU Medical College Institutional Review Board (IRB) before initiating data collection activities.
1.2 Researchers should submit their research protocols, including data collection procedures, to the IRB for review and approval using IRB form annexure 1.
1.3 Data collection activities should commence only after receiving IRB approval.
2. Informed Consent
2.1 Researchers must obtain informed consent from participants before collecting personally identifiable information.2.2 Informed consent forms should clearly explain the purpose of data collection, the nature of the research, potential risks, and participants' rights.
2.3 Informed consent should be appropriately documented and securely stored.
3. Privacy and Confidentiality
3.1 Researchers must ensure the privacy and confidentiality of research data.3.2 Measures should be implemented to protect the identity and sensitive information of participants.
3.3 Data should be anonymized or de-identified whenever possible to minimize the risk of identification.
3.4 Access to research data should be restricted to authorized personnel only.
4. Data Security
Following data security will be ensured during IRB approval:4.1 Researchers must implement appropriate security measures to protect research data from unauthorized access, loss, theft, or misuse.
4.2 Data should be stored on secure servers or encrypted devices.
4.3 Regular backups of research data should be performed.
4.4 Strong passwords and access controls should be implemented to protect research data.
5. Data Retention
5.1 Research data should be retained for one year period, and the plan must be stated in the IRB application form or funding agency guidelines in case the project is outsourced.5.2 Researchers should develop data retention plans and ensure proper archiving to maintain the integrity and accessibility of research data.
6. Data Sharing and Transfer
The data is solely the property of RLKUMC in case the research done at RLKUMC, however:6.1 Researchers may share research data with collaborators or external parties for legitimate purposes, subject to appropriate data-sharing agreements and legal requirements.
6.2 Data sharing should comply with applicable privacy and confidentiality standards.
6.3 Secure methods, such as encrypted file transfers or secure data-sharing platforms, should be used for data transfer.
7. Data Disposal
7.1 Researchers should securely dispose of research data and associated records once the retention period has expired or when data is no longer required.7.2 Data disposal should follow appropriate protocols, such as shredding physical documents or permanently deleting electronic files.
8. Review and Updates
8.1 After every three years data Collection Policy shall be reviewed, updated, and communicated to all relevant stakeholders to reflect changes in applicable laws, regulations, and best practices in data protection and privacy.